Introduction
This is something I am committing and putting my soul into, and this article will guide you and provide step by step instructions on how you can start selling drugs online. This is of course for educational purposes, but this is legit if you decide to use it.
Why should you sell drugs online?
The logical parallel to this would be, why should you eat healthily, why should you work out, why should you smoke weed or do absolutely nothing? You do not have to do anything, you have a human right to do whatever your heart desires, or not to. As long as this does not hurt lives, does not limit freedom or damages someone else’s property. This is your (if you want, GODS) given human right.
So let us rephrase the title here a little bit. Did a voluntary exchange of good hurt anybody? I do not think so…
Why should you sell drugs online? Because there is nothing wrong in exchanging goods, even it these goods are cocaine, MDMA, LSD etc… We are grownup intellectuals who can make a decision when it comes to making a choice, and making out choice illegal (I am talking on about selling drugs online) is a crime.
You are a criminal!
A criminal is someone who takes your goods using violence, power, and authority. Let me help you here. Police, governments, laws, FBI, and even Facebook… but selling what others need and want to offer a fair exchange for it is should not be a crime.
Morals?
At this moment you are probably yelling at your screen and comparing this to some other disgusting stuff you saw on “the Television” and read on some beauty blog. There are indeed some moral things you might have a conflict with, but this more about the utilitarian reasons for why you should sell drugs online.
This type of business can make the world a better and safer place. How? Imagine that you (who is probably not a drug lord) are living in a country where drugs are illegal and the only way to get some is to find a local dealer in a dark corner. Now imagine that you could order it online from someone who is a clean seller, who can even be your neighbor with 3 kids, a wife, and 12 cats?
The second scenario allows you to make a transaction without risking your life in that dark alley where you might as well get robbed, killed or beaten up by some random dude whose number you got from some online forum, or a beauty blog…
Is it safe to sell drugs online?
This is the case where a more positive than negative answer will apply. We understand that selling drugs online is not something you would brag about, therefore it is most recommended to stay one step ahead of the authorities. This indeed holds some risk, and I will try to mitigate the risks to a minimum in this article.
Key elements to stay anonymous
- Operations Security (OpSec)
- Online Security (Digital)
Anonymous Cryptocurrency Payments
In my previous article, we have discussed the end of Bitcoin Security Being a Myth, where the most recommended anonymous currency is going to be Monero. If you want to sell drugs online, then Monero is your cup of tea if you like it or not.
Monero has a hard-coded anonymity, which is why we will use ZION Market as an example because is uses Monero as the main currency.
This Guide Outline
To make this guide as understandable as possible, I will divide it into many sections and subsections with their own small tutorials and guides. It is important that you follow and dive in the steps and information, as this can save your life.
We will be using different software, so please read carefully about the installation and execution of each software.
You have to know about:
- TAILS – This is a secure operating system which we will be using in the tutorial.
- PGP (Pretty Good Privacy) – Read about encrypted Communication
- Another good source from Pittsburgh University
- Monero – A detailed guide about the coin
Even though I will try to be as straight to the point as possible with this guide, I still recommend reading much more about Operations Security and digital security in general. This is especially important if you are planning to sell drugs online. Darknet is an amazing thing, not a typical place for an everyday user, but it is monitored excessively by authorities.
Most important part of this whole guide is to stay safe, protected and secured on the interwebs. Think about yourself first. Do not know how to emphasize it even more but read more than just my guide recommended sources. This will pay off when you have your Darknet Drug Empire up and running.
Operations Security (OpSec)
This is a must know for anyone who is working cybersecurity, but in short Operations Security is a method in which you approach data and information protection. In its cor,e it is a 5 step process where you identify critical information leaks which can lead to exposing the victim if it is a person or an organization.
In other words, look at OpSec as a methodology where you as a user protect yourself and your data from being collected from different sources which if exposed can make you “visible” and approachable by authorities.
A perfect example would be the world-famous story of Ross Ulbricht and the SilkRoad. (I highly recommend reading and watching documentaries about this guy and what he did)
SilkRoad Operations Security Fail
Mr. Ross was a person behind the largest darknet drug (and not only) selling market on TOR. The market was shut down after an ongoing investigation found some traces in 2013 which lead to Ross.
Case:
- An FBI after googling “SilkRoad” and “onion” and ended up on a forum.
- He used the forums filter to filter the posts to 2011 (right before SilkRoad became HUGE)
- He found a post name “A Heroin Store” and Bitcointalk.com
- Alias of the original poster was “altoid” with a link in his account
- Link redirected to a WordPress page with instructions how to get access SilkRoad (Just like this article tells you how to sell drugs online)
- The agent doxed the nickname and found a post where “altoid” was searching for “the best and brightest IT pro in the bitcoin community to be the lead developer in a venture-backed Bitcoin startup company.”
- Braking point – He used his personal Gmail in the early stages of the process
Lesson to learn
Everything you put on the internet stays here, safe and sound, and can be used against you in court. Can be traced. Can be doxed. Can be traced back to you. Let us be a few steps ahead of that.
P.S. Ross is serving a life sentence for his victimless venture.
Mindset
You have to develop a mindset of being as anonymous as possible as this is very important and sometimes crucial part of survival. Keeping anonymity is important not only using different software but as well hardware.
Cannot emphasize that safety is a very crucial part of what we are doing, this indeed can cause some discomfort in terms of steps which has to be taken regarding the approach of this process. But with higher levels of comfort, you are lowering your level of security and therefore have higher risks of punishment.
If you do not mind people going through your mailbox, then this is a mindset you must change. Think of the fact that people searching your mailbox or mailman is delivering you dildo magazines which have your name on it. This is the level of concern you must have in this business. You must think in terms of no one has to know or have interest in what is in that mail, only the person it is intended for.
Your goal is to keep high levels of OpSec stay anonymous and separate your online personality with your real life so there is absolutely nothing connecting you in real life from day 0.
Operation Security Tips
- Never use your real name (duh…)
- Never use a name you have used before
- Never use a nickname previously used by you or is somehow connected to you
- Never tell anyone or login with there new credentials in front of people (be alone)
- Never tell anyone (do I even have to mention this?)
- Communicate using ENCRYPTED only communication
- Never use a camera monitored public space or place to do your dirty thing
Online Security
Now when you are aware of OpSec and have the right mindset, be ready to make some investments which are going to represent everything that was mentioned earlier. You have to get a new phone. When I say new, I mean NEW, because it should have zeroed history and have no trace of the previous usage.
Never show your new device to anyone! See tips. You have to create a new identity. Are you an android user? Buy an iPhone, cheapskate…. Be different… And do not brad about it. I mean, you got the idea. Oh yeah, do not put your moms’ number on the new phone or order pizza from the new phone (do I really have to emphasize such things?).
Always use TOR and TAILS. TOR should operate on a non-persistent installation of TAILS. You probably know now that TOR is using .onion domains which are operating majority of darknet markets and are used to sell drugs online.
If you are hearing about TOR the first time and still have no clue what is TAILS, delete your internet, shut down your computer and go get some fresh air.
SHOPPING!
We need:
- New smartphone
- Pre-paid SIM card with internet data
- Stock (drugs and narcotics of course)
- Laptop
- TAILS OS on a memory stick
- Label Maker or printer
- Shipping supplies (packaging, bags, tape etc)
- Monero
Hardware
Remember, you have to be someone you are not and stay anonymous and using your credit card is probably going to land you in jail pretty quick. If the police in case of something is going to trace your hardware which you were using for selling drugs online, sorry, your own fault. The goal is not to leave a digital trace. So, use cash, please. Preferably withdrawn where you were having a beer in a pub.
Laptop
Nowadays laptops are pretty cheap, so go ahead and get some low-end computer and it will be enough because our software does not require a lot of computing power to run.
If your local shop will ask your name, address or phone number, give them fake information. By law, you are not required to give them your ID. They ask it for advertising data and refunds anyway.
Please do not buy your hardware from your friend Tim who works in the electronics store… We want to keep you as anonymous as possible, and better wear clothes you usually do not wear in public and wear a cap/hat. Chances that you be caught only because of this, but this is a great step to avoid future paranoia.
Do not use a previously used laptop. We need something with no previous digital traces.
TAILS OS on a memory stick
I mentioned this in the beginning but here you go
Label maker or printer
Why? Well… You can use a printer; the only idea here is you avoid writing labels by hand when sending drugs.
One thing to consider here is that if you have some super advanced printer, it can be traced, somewhat. Some printers have a “feature” which is called “tracking dots” which can lead back to the original printer. To be sure, check if your printer is mentioned in the EFF (Electronic Foundation Frontier). If you have to buy a new printer, please use cash….
Smartphone
Similar case as with the laptop. Do not buy it from Tim and use false credentials. Pay with cash. Get a new one, because it has no traced used data.
I personally recommend Android over iPhone as they are factory encrypted. Just do not buy a smartphone which is too old, as it might not support up to date encryption.
Put all possible passwords on your new phone which are NOT 1234 or your date of birth.
Do not use your new device for calling, it will serve as a hotspot for internet sharing. Consider it to be your modem.
Perfect case scenario, do not take your 2 phones with you when you are planning to do your dark stuff because they both can be connected to the same GSM and this might connect your criminal phone with your phone as you were at the same place at the same time.
Obviously, you should not connect your phone to your private Wi-Fi, or any other hotspot. Same goes for your laptop.
Prepaid SIM-card with internet data
Do you really need an explanation regarding why you need a prepaid SIM card? Yes? Well then… You should avoid registering your name with your new number. In some countries (like the Netherlands), you can get a free number from a guy on the street who is giving them away. Or some small kiosks in shops where they do not ask you to register.
Better option to ask someone to get the prepaid SIM card for you with the data, so you do not appear on any surveillance cameras.
Let us assume you have your phone up and running. Now forget to use it for telephone purposes. This means no calling and no text messaging from the phone because we do not want to leave a digital data trace. Even if you ordered pizza with the phone, you are giving a lead to the authorities. Never give anyone your phone number, because any connection with it can lead to revealing your true identity
BEST CASE SCENARIO:
The biggest recommendation would be to change the number on a monthly basis. The reason for that the authorities can trace the uptime (live signal) of the phone. So not only changing the SIM cards will help, but also changing the location where you are using it. When I say different places, do not make these places in walking distance from your home. Remember that you have to act like you are someone else, a new identity.
Internet connection and WIFI adaptor
Using your phone as a hotspot is an amazing way in terms of portability and ease of usage. But there are some really critical downsides to this. While using your phone as a hotspot for one purpose only, you are aligning the connection time with the time your sales account is being live while selling drugs online. Quite a nice coincidence, isn’t it?
Imagine you got caught (which you will not if you are using my methods), and the data provider sees that the data transfer was used mostly through a secured browser TOR. I mean, does not prove anything, but then we connect the being live on your sales account and being connected to TOR and we got ourselves very nice pattern to investigate.
Another great alternative would be to use open routers (which is a very hard thing here in the Netherlands). You can buy a small external WIFI adaptor which you connect to your
computer through a USB port. It makes the connection read the information from the adaptor rather than your computer, and then you connect your computer to this adaptor.
The best choice would be this adaptor which was tested by Freedom Activists.

Phone Method (Not Recommend)
Something I do not recommend but might be an option for you. You can hide your phone which is connected to a power source and has hotspot turned on and enough data. But in this case it has to be hidden pretty well, so during a raid, it will not be found, and it should be protected with a password. Wifi and phone. Both. Okay?
Drugs and Narcotics.
Well, if you would really like to use this tutorial, you probably figured out this step.
Shipping supplies
This is another very important and even crucial part you have to take into consideration because the level of stealth here has to be “Top Notch”.
Requirements:
- Envelopes
- Rubber gloves (disposable)
- Vacuum bags and machine (this is an amazing machine)
- Spirit or any other alcohol to clean your workplace after packing
- Face mask (if you are selling something that requires a mask)
- Workspace
How do I sell drugs online?
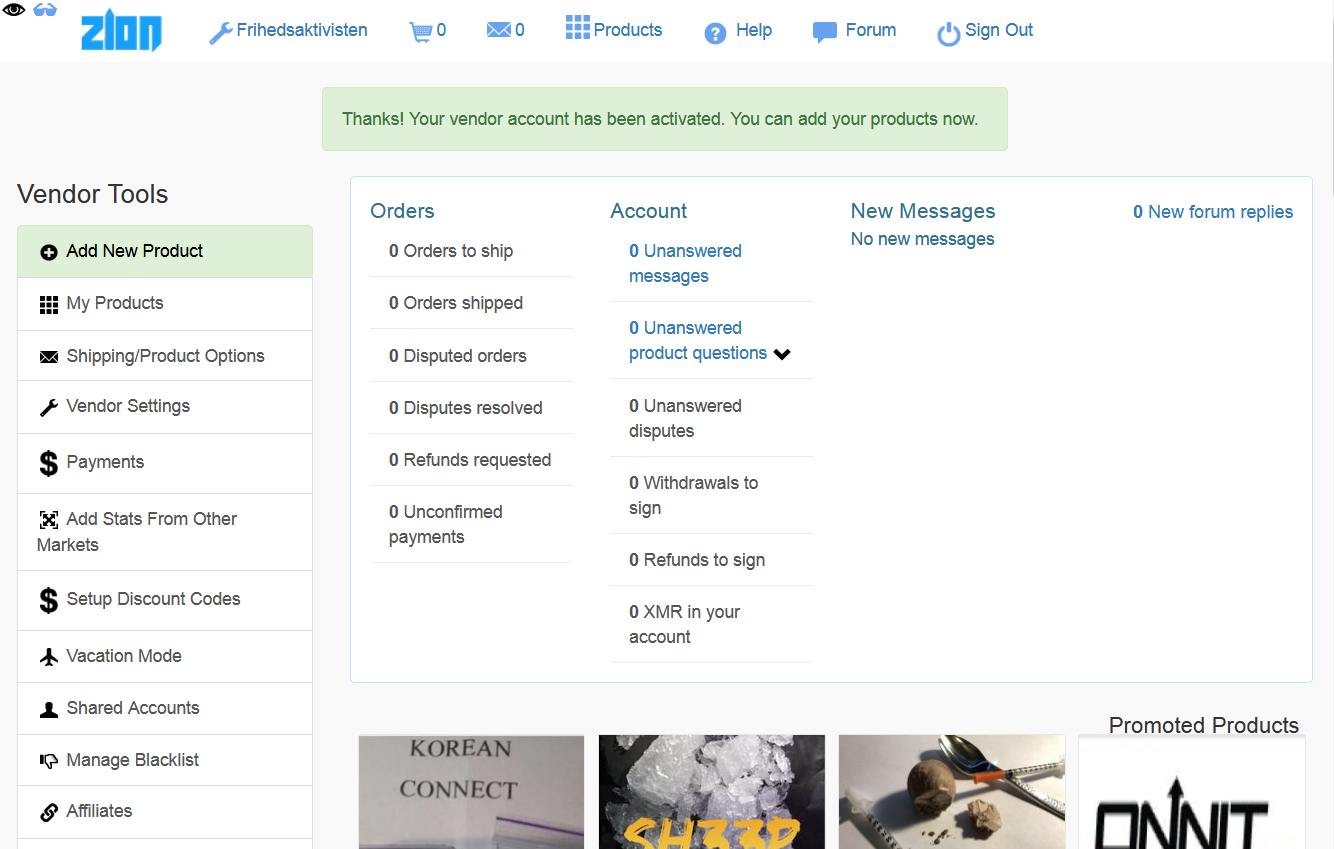
Launch TAILS and TOR and navigate to Reddit Link where you can find all the redirecting addresses to Zion. The market is running using the latest TOR v3 protocols which means that it is a fast loading website in comparison with other markets online.
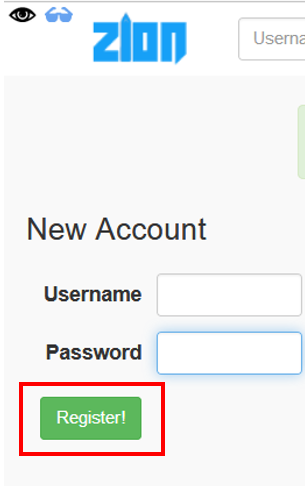
Navigate to the website -> Complete captcha -> Create an account (Register)
I really hope you still remember the OpSec lesson above and did not use your real name when creating the account. Same goes for the password, please do not make it your date of birth jeez…
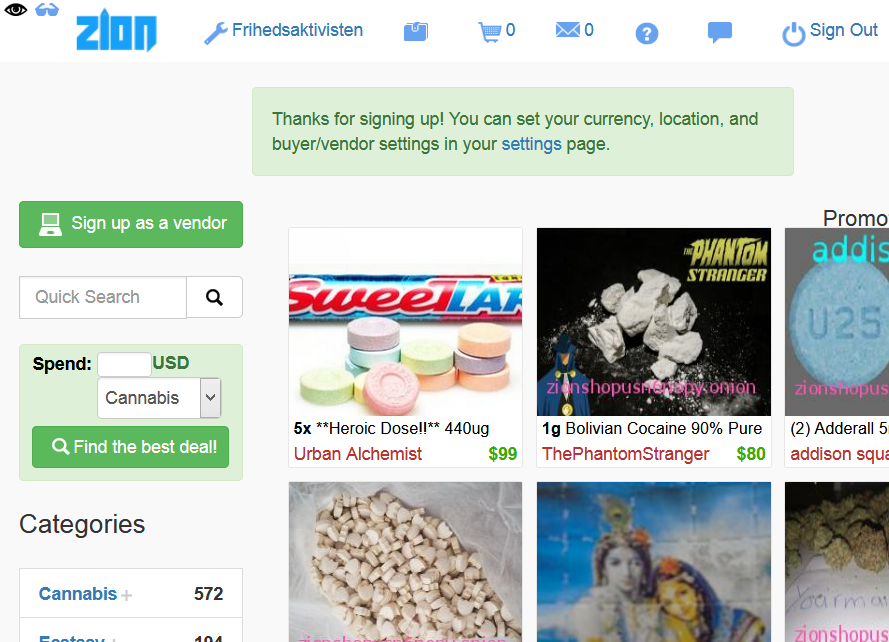
User Experience on drug markets are the same as on Twitter, therefore navigate the “Sign up as a vendor”. The faster you click, the faster you will become a drug lord.
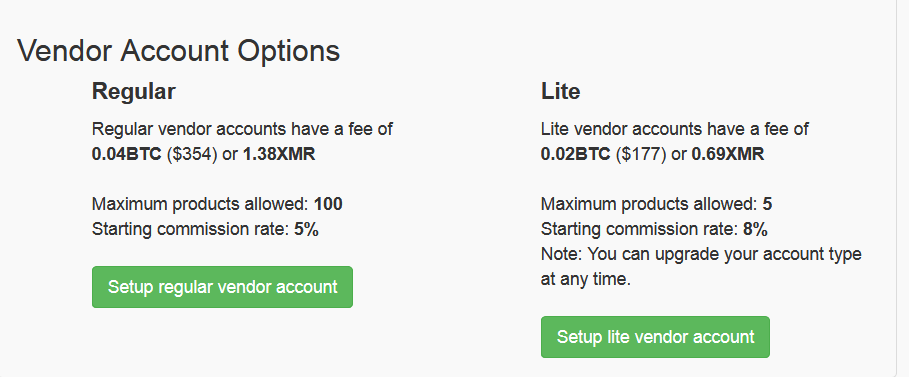
If you are not a drug lord yet, go with the “Lite Version” of the store. If you have plantations, then sign up as a regular drug seller. As mentioned above, the beautiful thing about Zion is that is works with the most anonymous currency Monero. So set up your account and pay using Monero and add Moreno to your accounts balance.
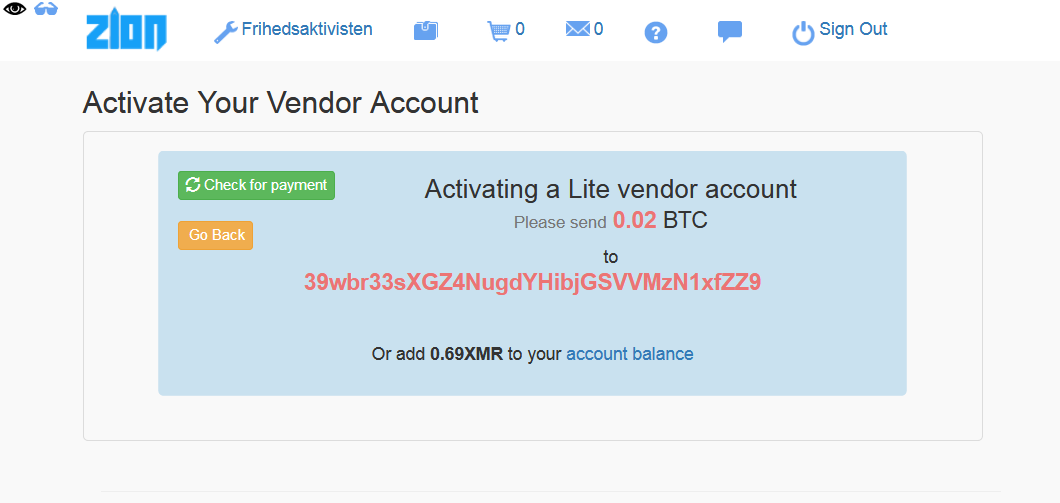
To be able to transfer Monero to your account, you have to set up a PIN which you will use when you will be cashing out from Zion. The transfers usually take a minute or two.
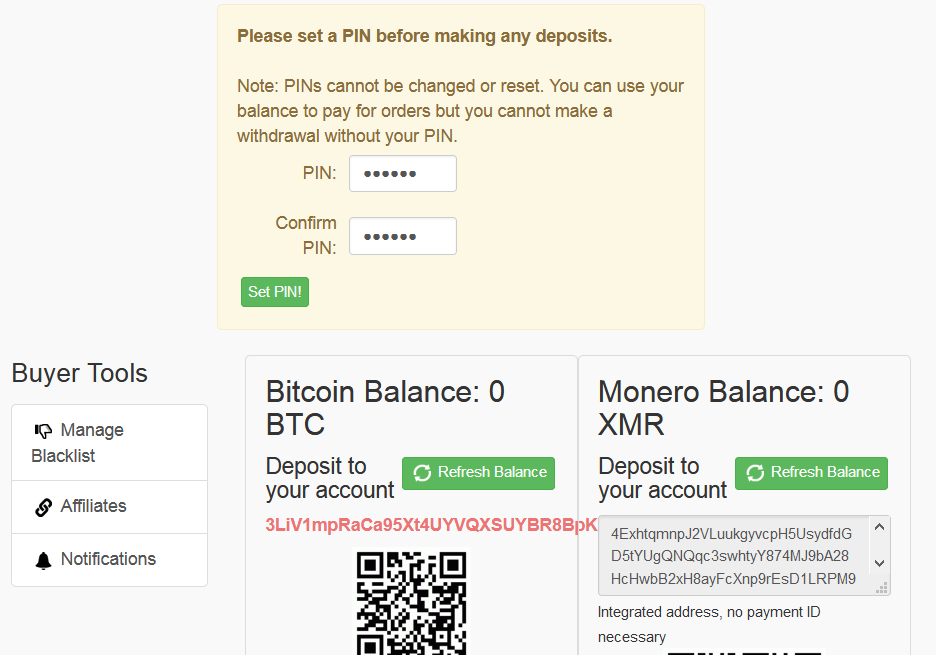
When you got some Monero on your account and created a PIN, we must repeat the procedure by signing up as a vendor again in the top left corner. After that finish setting up the account by filling in some information regarding your market.
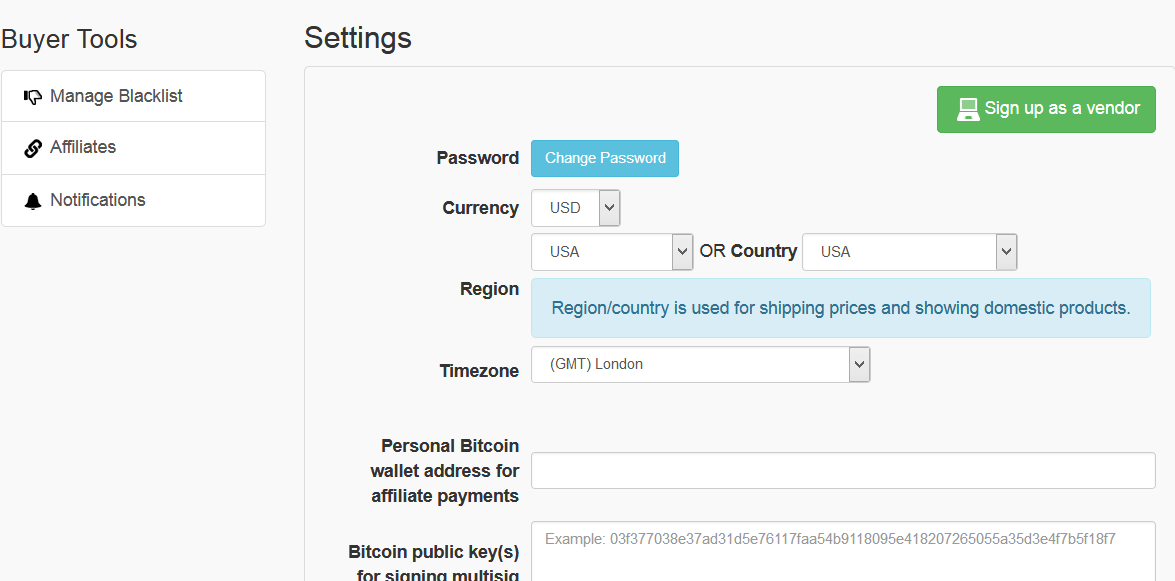
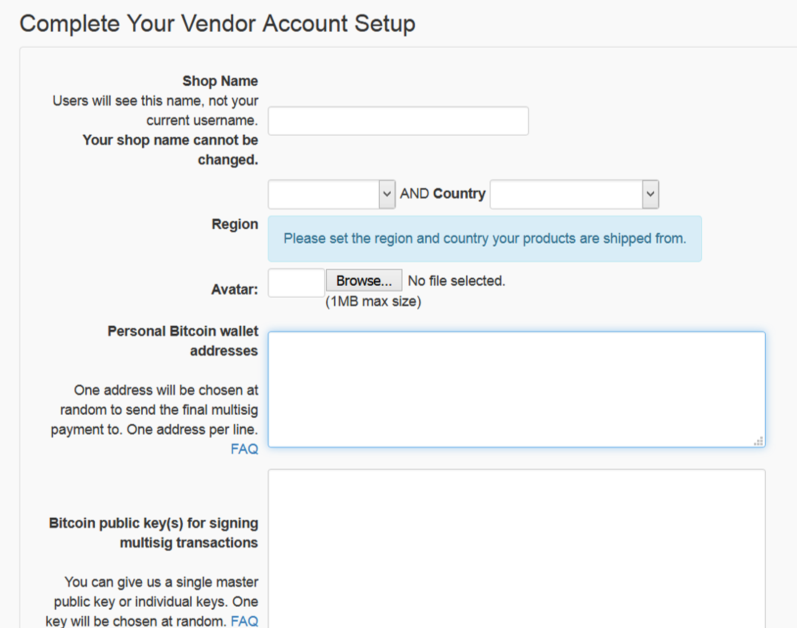
Note: Enter a bitcoin addressed, as it seems to be a mandatory field by the system, even though we are going to use Monero.
If you do not have a Bitcoin wallet, use TAILS to run Electrum Wallet and create a Bitcoin Wallet and a Public Key for the Multisignature.
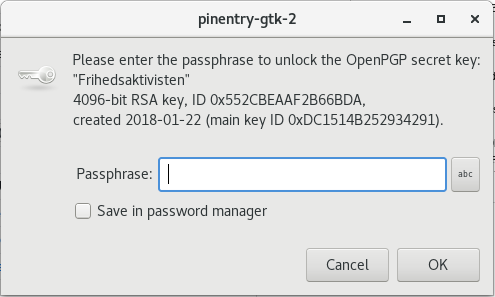
Enter your PGP key and complete your signing up as a vendor.
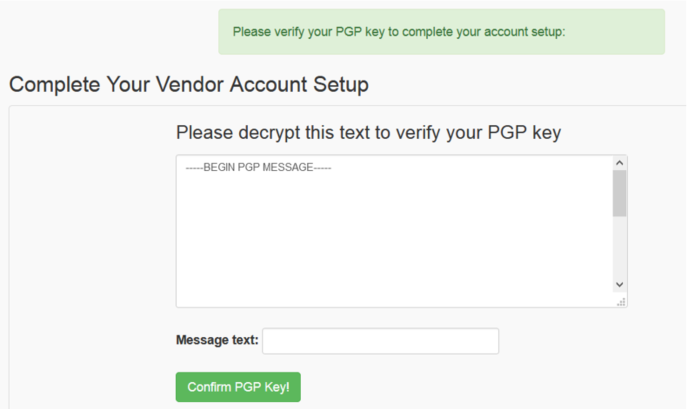
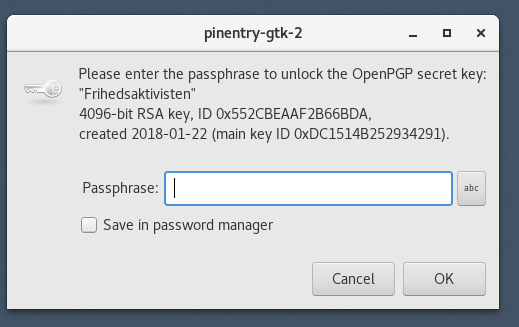
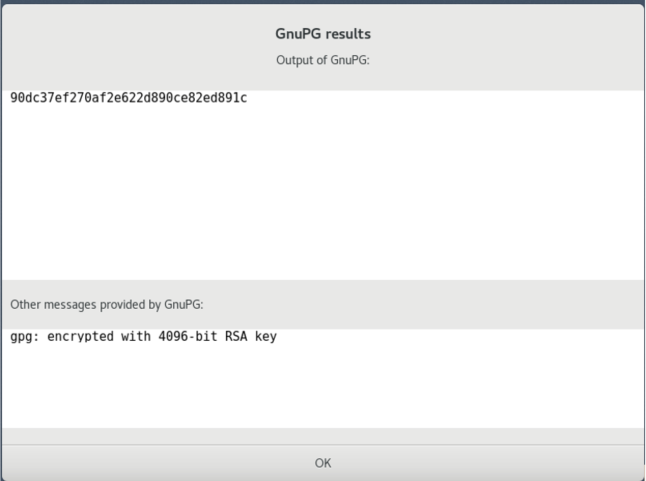
You should have received a PGP encrypted message from Zion which you have to decrypt to get the code.
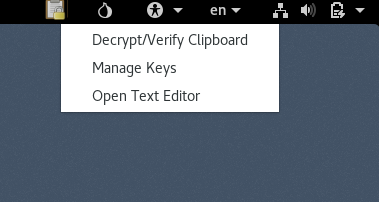
Copy the code, navigate to the top left corner where you will see the Clipboard being changed to a padlock. Click on Decrypt/Verify Clipboard and enter your copied PGP code and click ok. This will decrypt the message which you will have to copy back to the Zion market.
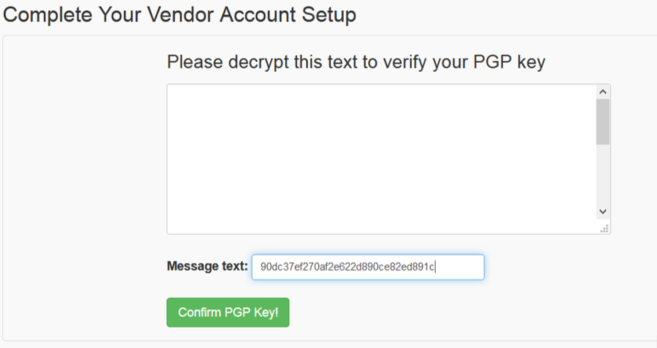
YOUR VENDOR ACCOUNT HAS BEEN CREATED
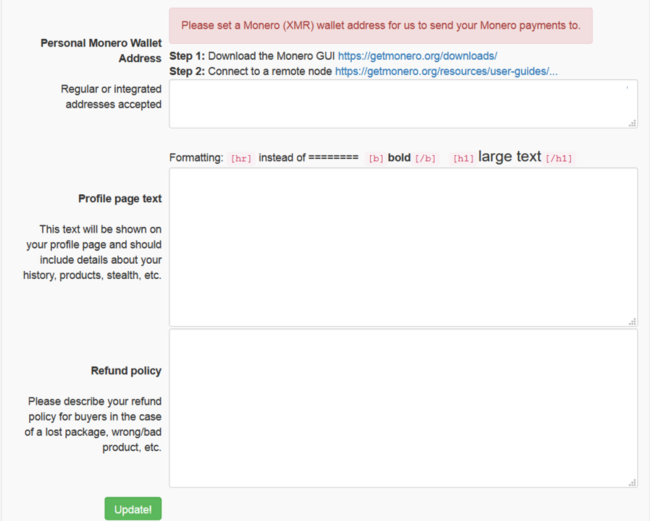
Navigate to “Vendors Settings” on the left and continue filling in the necessary information for your online store.
Important Sections:
E-commerce
- Setting up an attractive profile page
- Refund Policy (yes, we need it as well)
- Product page setup
- Targeting
- Product Description
- Shipping
- Encryption (PGP key)
Profile setup & Refund Policy
- Include an attractive description of your shop and what you are doing, can check other profiles for inspiration.
- Refund Policy is important, but most of them do not offer refunds, that is why you should offer the best product to avoid refunds being a thing.
- Update your description and add a new product
Product page setup
- Description of the product must be very accurate and attractive, including practical information about its use (depending on what you are selling)
- Targeting must include the countries you are shipping to. A great indication can be the Language you write your description (Russian for example)
- Select the relevant category for your product to be found more easily
- ALWAYS requests PGP-encryption of all sensitive data and shipping address format
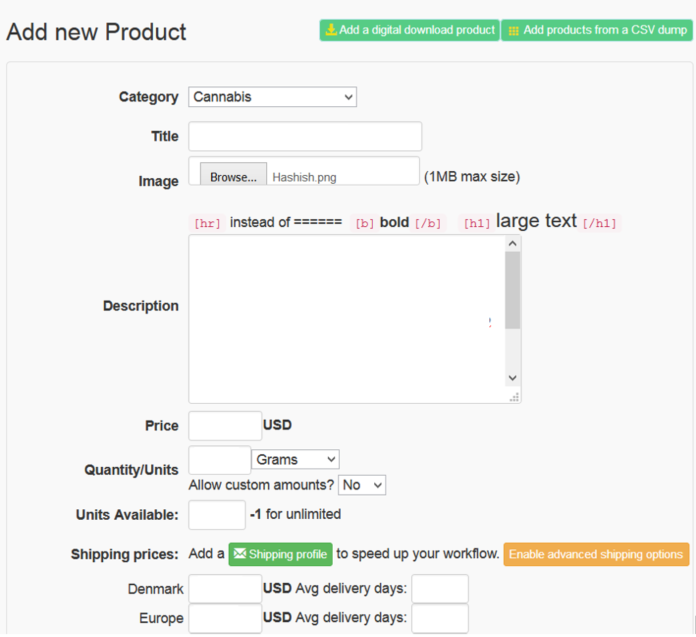
Operations Security
- Do not take product pictures where you are holding it while smiling and exposing your face to the rest of the world
- Never show faces in an image
- Avoid reflections of people in the photo
- No people in the pictures
- Do not upload photos from a recognizable place or well-known background.
- Do not show exposed fingers and hands to avoid fingerprints being read from the photo (yes you can do that)
Great example for inspiration would be other vendors on the market, where you can copy what suits your profile of work. As well as comparing yourself with the competitors in the same region and offering a better service, products or simply better communication (Content and Photo wise).
Select the currency and add the prices of your products in order for your buyers to transfer Monero into EUR, USD etc. Please do a competitive analysis before setting up an insanely high price. Start lower as a new vendor and increase prices over time. Gain reputation and recognition first.
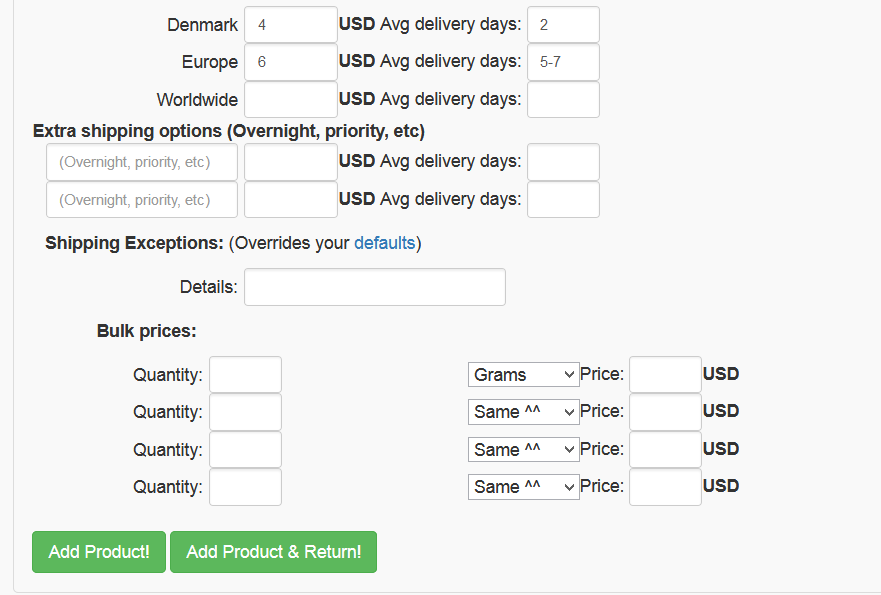
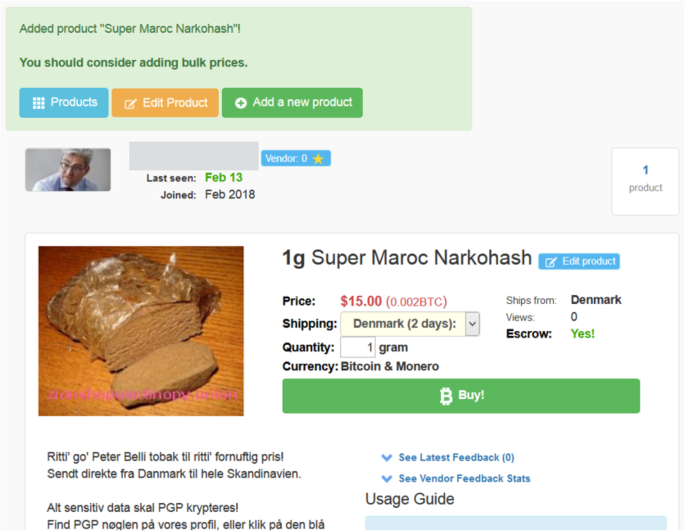
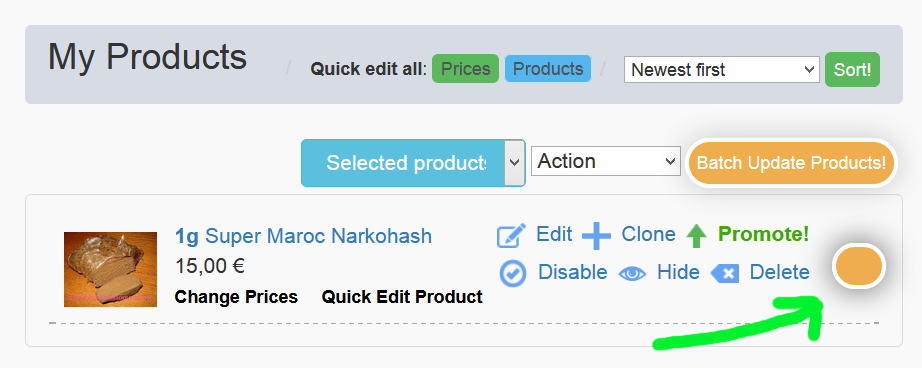
In order to make it visible to the buyers, you have to activate the product by navigating to your products and in the drop-down menu above the product which says “action”.
The path: Action -> Enable -> Batch Update Products (this is useful if you have more than one products to make sure your store has all product “live”)
This is the moments of excitement of any entrepreneur where you wait for your first order to be placed. Login after some time, maybe 3-7 days and see if you received any orders from fellow clients.
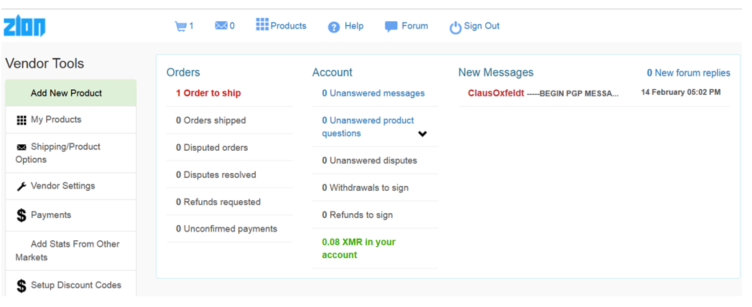
If there is a sale, navigate to “1 Order to ship” where will see all the orders.
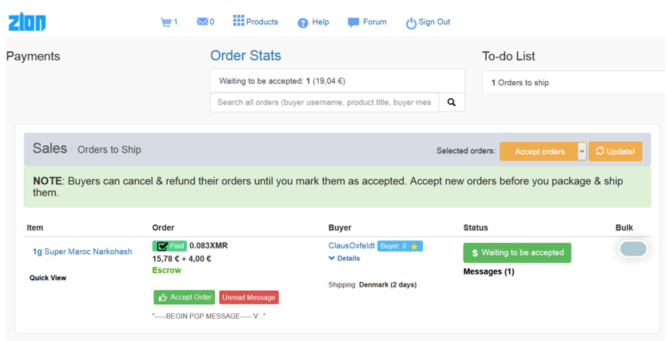
Firstly, do not click anything before you have reviewed the encrypted PGP message which the buyer should have provided. This is important because if you have a very specific shipping and the country focused business, a person might not have taken all the criteria into consideration and purchased the products anyways without you being able to ship it there.
Secondly, click on the “Unread Message” and copy the PGP key. Navigate to the padlock in the clipboard button (just like we did previously) to decrypt and verify the PGP key.
After decryption, you should see the address to where you would like to deliver the goods.
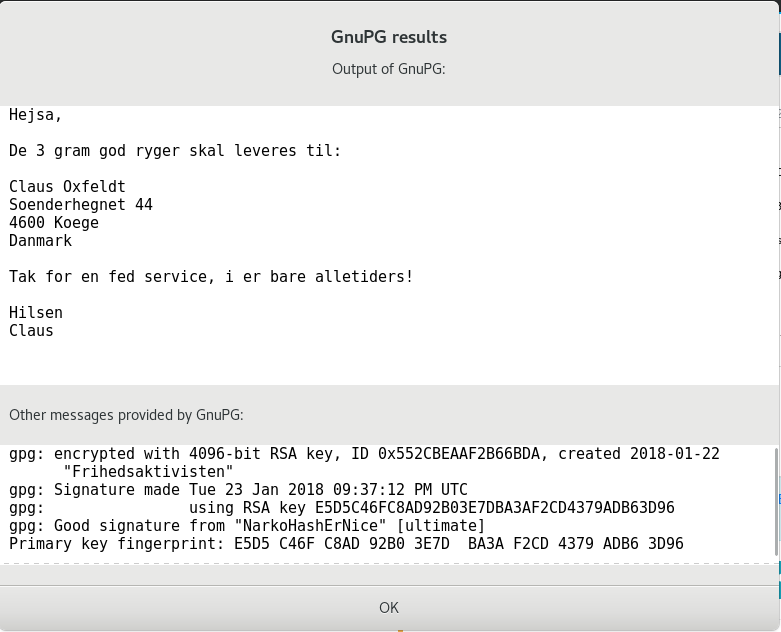
You should see the address and move forward with the order as soon as you feel you can fulfill it.
Navigate back to the website and click “Accept Order”. Another recommendation would be to communicate with the buyer, as there might be some details which should be discussed. Use a PGP key to communicate, and never just text.
Shipping
Shipping of goods and preparation:
OpSec:
- Alcohol (spray)
- Gloves (silicone, one use, disposable)
- Workstation (easy to clean, preferably a cover to just trash)
- Disposable clothes or cheap apron
- Plastic bags (large trash bags)
The crucial part of the packing process is not to leave any DNA or fingerprints. By no DNA, your sneezing and coughing leave DNA traces as well, so use a mask and not clothes where your cats’ hairs are not going fall on the products.
After you will complete the packaging process wipe, clean all the fingerprints even if they are not yours, they might be from someone at your local store downstairs which will ultimately narrow the investigation which holds a risk for your business. So spray/wipe/rub the envelopes, packaging to remove all the DNA, fingerprints and grease from the KF next door. Do not, lick the stamps, ok?
Get your equipment ready!
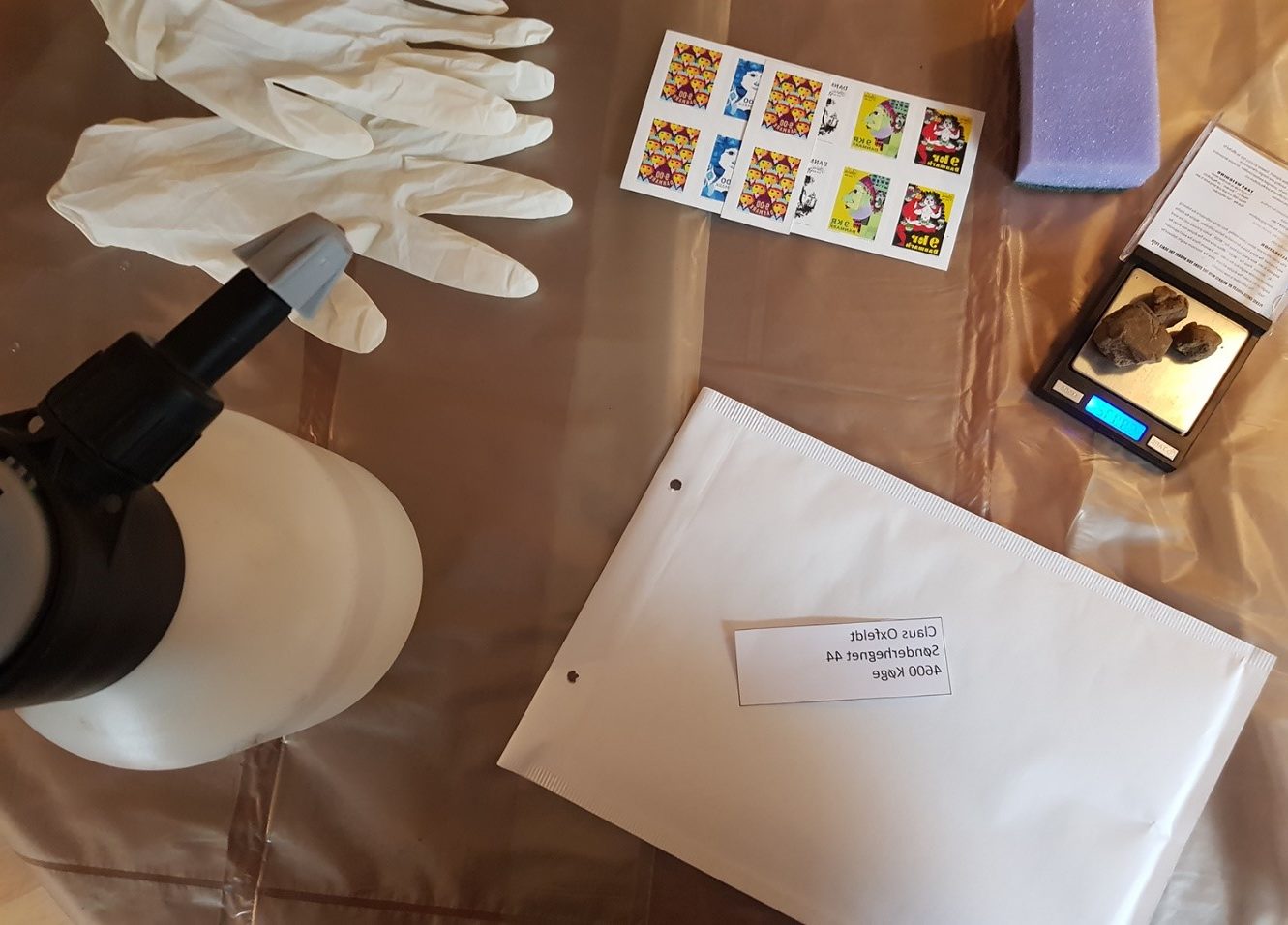
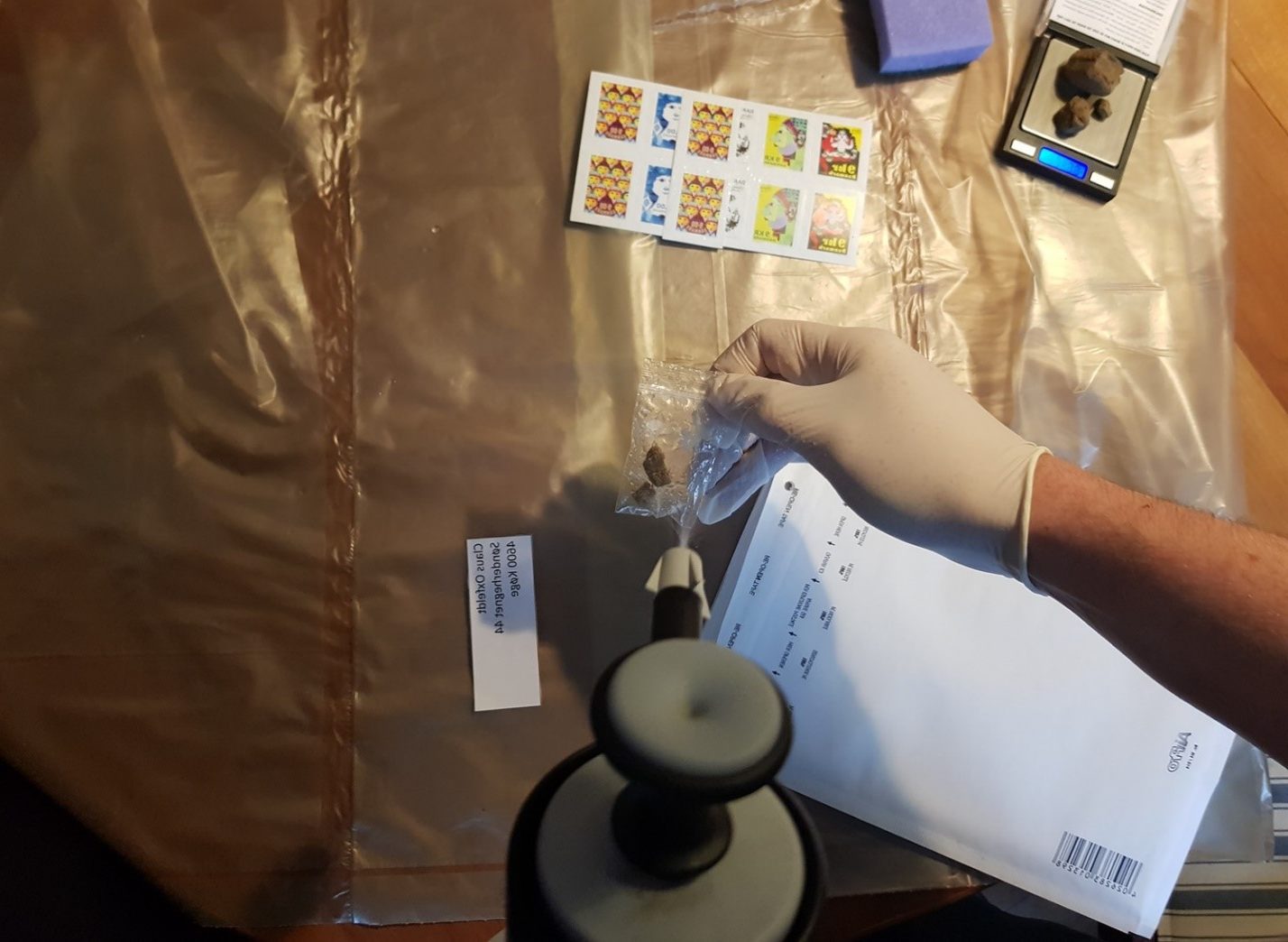
This is your first step to perfecting the art, so keep in mind that after you will deliver your products locally and feel comfortable in what you are doing, you can start sending this out to the rest of the world. You might want to use a sponge soaked in alcohol to wipe the packaging and/or if you break a sweat.

Mailboxes
Never go to the post office to send the package, because they have surveillance cameras which can trace back you. Pick different post box locations in your city and drop the packages there. Do not touch the packages with your hands, do not carry them around. Put them in a clean bag when you are leaving home and then just chuck them from the bag into the postbox. Can use disposable gloves if some post boxes are not easily accessible.
After dropping the products go back and login to your market and mark the order as shipped.
Zion is an amazing market which uses Escrow which might take a few days for the transaction to occur and Moreno will be transferred to your account. The process behind Escrow is secure and will transfer you the money after 3 days even if the buyer will not confirm the delivered package on his end.
If your business will explode and you will feel a little bit like El Chapo, you can pay 500$ to be able to finalize your orders as soon as the order is placed and the buyer transferred you Monero. Is it worth being credited right away? Yes. Do you want to pay half a grand for it? You decide.
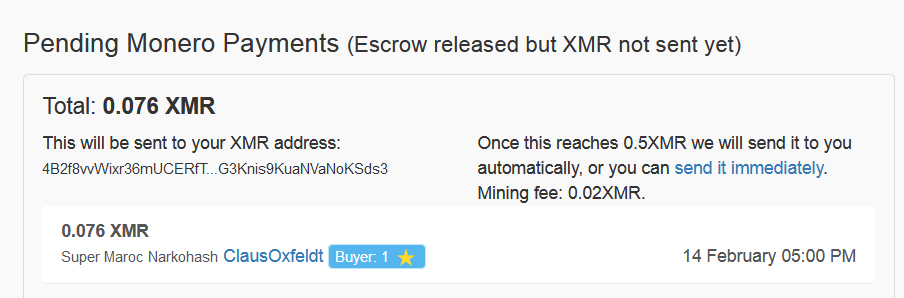
Monero will automatically be transferred to your provided wallet after you reach 0.5 Monero on your account on Zion. This automatic transfer ensured that you will always get your money. If Zion shuts down tomorrow, the max amount you will lose will always be under 0.5. If you cannot wait, just click “Send immediately” and get your Monero right away.
Confraternities, first sale complete. Feeling the hype? The Adrenaline? The Possibilities? The happiness someone will get from your product?

Data removal from images
In the cybersecurity world, this is one of the first things that is getting checked when searching for a person or exposing a phishing account. Ethical hackers are looking and investigating the data which is getting saved on any image taken. In this case, you were probably taking photos of your products and uploading the images to your product pages. That image holds data which literally can lead the police right to your front door.
Any camera, digital or phone camera includes such data as resolution, date, time, camera model, and GPS location. This data is called EXIF-data. This is why you should take this step very seriously when you are uploading images to the market.
This is very easy to remove in TAILS:
Navigate to: Applications -> System Tools -> MAT (Metadata Anonymization Toolkit)
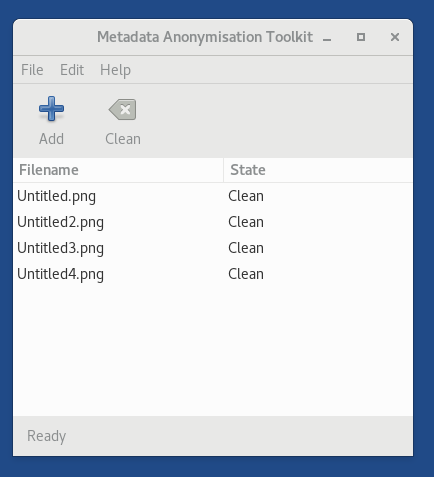
You can drag the images to the toolkit and click clean to erase the data from the images. Keep in mind that you are only able to save the images in TAILS folder “Persistent”, because that is how the OS is designed.
Psychoanalytical analysis
Every person in the world has a different style of writing. If you are writing in a non-native language, it complicated things when you want to stay anonymous, because some saying and phrases are not translatable or are used only in one language. Some languages are some prone to make specific grammatical mistakes in specific words and phrases, and it happens much more than you think.
If you thought already of a perfect sales pitch for your product, kill it, delete it. Write your text all lowercase or all caps, with no punctuation and stick to short sentences. Avoid your writing personality as well.
Should I buy a Lamborghini?
You can, but the important part of spending your money is to do it correctly. Money earned this way are not the same when you have worked at McDonald’s. Being mindful when spending this money will save you jail sentence and a lot of nerves avoiding every night paranoia. Few ways to go from here.
Cryptocurrency debit card
If you have not heard yet, this is a great business model and interesting industry to read on. Banks and separate companies now offer debit cards which can be connected to cryptocurrency exchange and directly to a bank account. This is a great way when it comes to sending your hard-earned drug money (usually Bitcoin) to a fake company address and then withdrawing the money.

This is not such an easy task to have such cards anonymously, as they 100% of time required to have it connected to an ID, passport or address. I am not saying that you cannot fake an ID, passport or an address, but we want to make it look as legit a possible. It is difficult NOT to leave a trail when transferring larger amounts, and not only difficult, it is also dangerous for our case because we are not buying 3 tons of donuts, but trying to run a narco business here.
Crypto ATM
In the Netherlands, there are a few bitcoin ATMs that give cash for Bitcoin. Might be a travel for some people, but this is a great solution if you need some quick cash.

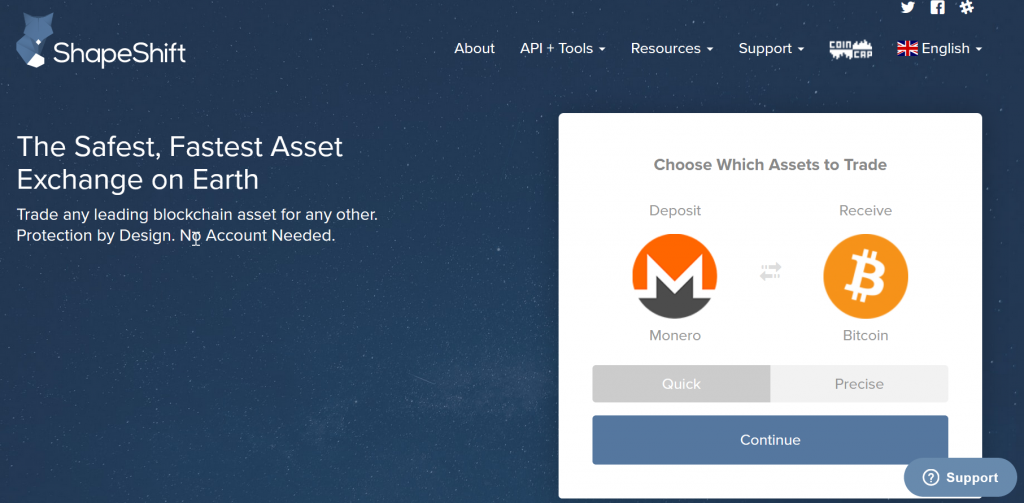
Monero – Online exchange
There are 3 most popular cryptocurrencies which are widely used and are easy when it comes to exchanging, they are Ether, Bitcoin and of course Monero. A very practical solution for easy an fast exchange service is Shapeshift
Now I can buy a Lamborghini?
If you have everything set up and working to stay anonymous, you are pretty much welcome to spend your money any way you want. Some countries are okay with people spending specific amounts a day.
The Netherlands allows spending 10.000EUR a day with no control. You can walk around and buy yourself a lot of ice cream and nice clothes if you are into that. Do not be scared to live a little with your hard-earned money! Some people live very comfortably from cryptocurrencies humbly drinking coffee for 2.50EUR.
Is there a risk of getting caught?
We went in detail through how to keep yourself anonymous online, TAILS, TOR, Crypto, OpSec etc. And after all this, you ask if there is a risk? Well, good catch, because the answer is YES
I have never said that this business is not risky. By following the steps mentioned in this “Manual” or we may even call it “Tutorial” can mitigate the risks to a bare minimum, but there is always a risk. Statistically, you can get eaten by a shark, or drawn in the sea, or your bathtub. My point is, there are risks in everything.
Look at this manual as something educational yet be ready to go to jail if this business is something you want to commit to and live a rich life and become the next Pablo Escobar of the Internet. “Don’t do the crime, if you can’t do the time” – Urban Dictionary
Trust issues and Mitigating risks
Selling drugs online is a much safer environment than being a black person in America trying to buy roses. Biggest risk in this business comes from gang shootings, junkie hobo customers on the streets, putting your face our there and in general standing in a dark dirty corner to sell the dope. This method is a great step up and advantages which focuses on more sophisticated users.
In the online vendor community there are many discussions regarding customer trust, yet the online world we must trust blindly, yet the phenomenon of it working without having any contact with the vendors and customers can be a great example for some legal businesses. The average online customer in this industry is usually more professional than an average customer in Walmart.
How to be sure that I will not get raided?
You cannot be sure. Highest risk would be when your products is getting to or from the supplier. Imagine getting caught while holding 1000 pills of MDMA in your hands. You do not need a high IQ to understand that your place would be raided after 10 minutes after you being caught.
Operation security reminder – do not keep your equipment in your house, otherwise, next stop will be jail.
If you were working from home, you still have a chance to minimize the splash effect and your prison sentence. If you were encrypting all your devices, do not have a digital trail and kept your mouth shut, the police will have a very hard time connecting you to your sells. Being caught is not where we want to be, but this is something that can save you a life sentence.
Another Reminder – Do not run your business by paying with your own bank
This can lead to your house and might get the authorities interested in your persona, which is what we want to avoid at all cost. Which is why running your business from a different address (not your private one) is so crucial. The goal is to make the investigation a complicated as possible and keep your mouth shut.
Exit strategy
Paranoia can be a silly thing, but sometimes it can be a lifesaver, which is if you have any suspicion of an investigation, you should have an exit strategy which you can strategically follow.
Some situations for exiting the business:
- Your landlord being interrogated
- Your job employees are getting interrogated
- Your friends receiving strange calls or being interrogated
- You see police following you or people with a headpiece
- Just want to exit the game
This shortlist can, of course, be extended of you can have your own reasons to backup, but in any case, you need to have an exit strategy to avoid being backtracked later. So, do not throw away your kit into your trash bin, but if you want to do so, let it be someone else’s bin or the one far away.
Before you throw it away, clean the DNA with alcohol, remember the OpSec lesson. Better off, burn everything. The phone can be burned as well, but just drown it, or pull piece by piece apart and dump it in different bins.
Social Engineering and Public relations techniques (if caught)
Let us assume that you were caught by the authorities and are now being interrogated by them. What do you do? What do you say? Do you just spit all the information out? How much do you want to say? Well, there are a few facts and practices which are super simple and can save you from ending up in jail.
The majority of cases against criminals are constructed on the information which the criminals have provided themselves. This means that you just have to keep calm, be silent and do not incriminate yourself by acting stupid.
Some interrogation techniques can be very serious and very pushy, psychologically they can break you down, some people break in 30 min, some walk away as free people, your choice. But do remember one phrase which can save your life and repeat it again and again:
“I DO NOT ANSWER QUESTIONS”
This phrase is going to work if you are located in the western part of Europe because here you do not have to testify against your own personality which is stated in the Administration of Justice Act. If you are located in another country, please look into the possibilities of your countries act and legislations.
This chapter is very similar in logic with the “Operations Security” chapter, as you have to develop a mindset where you are not yourself, in order to do that, you should obtain some skills. People in their core are very emotional people and the exact same emotions are leading our lives and leading a lot of people to jail. Great cases which you probably heard about people confessing to the things they have not done, which is a very interesting phenomenon where the authorities break people into saying what they have not done. This is why you have to train a skill to actively fight the urge to confess to anything.
The social engineering techniques which are used by the authorities include searching for moments where he will be able to connect with you on a personal or interpersonal level. Asking generic questions and offering you a cup of coffee. Recognize the act? A good cop he is.
Recommendation: Keep your answers short and simple “Yes”, ”No” or “I do not answer questions”
This might seem as a very unnatural conversation, which it is, which is why you have to practice you Yes and No to make it as natural as possible. This is done to avoid engaging in any conversation with the authorities, which might lead to something you do not even realize. So keep is silent, short answers and be ready for unpleasant face expressions your way.
Brief Checklist
This is a very brief checklist for you to recap everything we have discussed here:
- Operations Security
- New PC
- New Prepaid Phone
- Memory stick
- TOR
- TAILS
- Cash for Purchases
- DNA Removal (Alcohol)
- No home WIFI accessing
- Do not tell your Mom
- Do not work in your home
- Do not use your bank debit card
- Do not use your real name anywhere
- Learn the phrase “I do not answer questions”
Conclusion
This business can be very dangerous and stressful but at the same time extreme and monetary compensating. This can sound great to be the next Pablo Escobar, but this is as well a very boring, cheeky and diligent work, and if you are not ready to do that and take the risk, then consider this as an educational material which is being practised massively in the world. Keep in mind, using torrents is also illegal and can get you jailed, but telling your prison mates that you were jailed for a torrented “Bee Movie” is not as cool as for being the next Pablo Escobar of the internet.